Baby RSA 2 (CRYPTO)
Category
Cryptography
Points
250
Difficulty
Medium
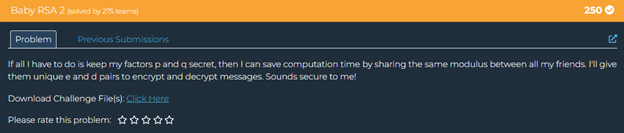
This challenge involves a common vulnerability in RSA cryptography called the "Common Modulus Attack." Let's first understand what we were given.
The Vulnerability: Common Modulus Attack
The fundamental security issue here is sharing the same modulus (N) across multiple users with different key pairs. This is a well-known vulnerability in RSA implementations.
The fundamental security issue here is sharing the same modulus (N) across multiple users with different key pairs. This is a well-known vulnerability in RSA implementations.
Why This Is Insecure
In RSA:
- The modulus N is the product of two large primes p and q
- The security relies on keeping the factors p and q secret
- The private key d is calculated as d = e^(-1) mod φ(N), where φ(N) = (p-1)(q-1)
When you share N but give different users their own (e, d) pairs, you provide enough information to factor N. This is because:
- For any key pair (e, d), we know that e·d ≡ 1 (mod φ(N))
- This means e·d = k·φ(N) + 1 for some integer k
- If we can determine k, we can calculate φ(N) = (e·d - 1)/k
- From φ(N) and N, we can factor N and break the encryption
The Attack Method
I used this mathematical relationship to recover the private factors p and q:
- First, I calculated e·d - 1 = 950636936352204...083788, which is a multiple of φ(N)
- I estimated k ≈ e·d/N ≈ 7982, and tried values around this estimate
- For k = 7983, I calculated φ(N) = (e·d - 1)/7983
- From φ(N), I found p+q = N - φ(N) + 1
- Then calculated (p-q)² = (p+q)² - 4N
- Took the square root to find p-q
- Solved for p and q using the system of equations:
- p+q (already known)
- p-q (calculated)
- With p and q, I computed the original private key for e=65537
- Finally, I decrypted the message
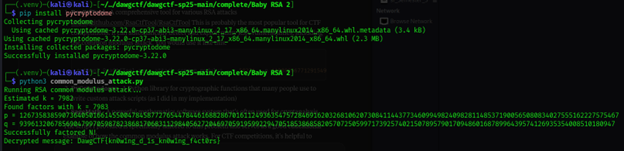
FLAG: DawgCTF{kn0w1ng_d_1s_kn0w1ng_f4ct0rs}
Key Learning: This challenge demonstrates why sharing the same RSA modulus among different users is dangerous. Even though each user has their own public-private key pair, knowing one private key allows an attacker to factor the modulus and break everyone's encryption.